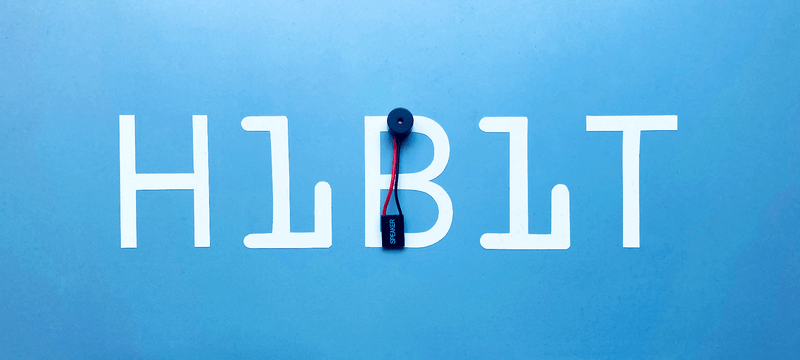
Buzzer is used to generate sound, beep or even melody of a song. It can be found in alarm devices, computers, timers and confirmation of user input such as a mouse click or keystroke. A piezo buzzer is not like a regular speaker that you might think of. It uses a material that actually changes shape when you apply electricity to it which in turn creates noise. The faster you bend the material, the higher the pitch of the noise that is produced.
Trending Now

How to setup Nginx server blocks (virtual hosts)
Nginx logically divides the configurations in order to serve different content into blocks. A server block is a subset of Nginx’s configuration that defines a virtual server used to handle requests of a defined type. Administrators often configure multiple server blocks and decide which block should handle which connection based on the requested domain name, port and IP address.
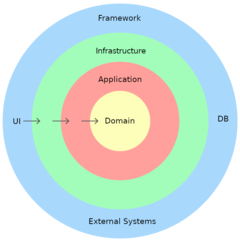
Domain Driven Design: Layers
Developing applications that can perform complex tasks can be a challenging process, and it requires careful planning and design. One approach to managing this complexity is to use a Layered Architecture. This architecture separates the application's code into layers, each with a specific responsibility and purpose. These layers are typically organized in a hierarchy, with higher-level layers depending on lower-level layers.
Premium articles
On-the-fly image resizing with Nginx
If you've ever managed a web server that serves images to thousands of users, you've probably run into the problem of serving the right image size to the right context. A 1200x800 hero image looks great on a desktop, but it's pure waste on a mobile screen or a thumbnail grid. The traditional answer to this has been generating multiple image variants at upload time, but that approach gets messy fast. A cleaner and more flexible solution is to resize images directly at the server level, on demand, using nothing more than nginx and its built-in image filter module. This guide walks you through setting that up from scratch, including caching so your server isn't processing the same image twice.
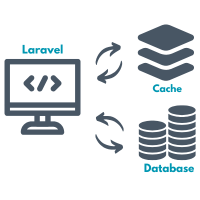
Tag-based cache inside Laravel repositories
Working with cache can drastically improve the performance of an application, especially when dealing with data that doesn't change too often. While Laravel provides solid support for caching through multiple drivers, it doesn't offer native support for cache tags. To work around this limitation, we'll integrate Symfony's Cache component, which brings tag support and fits well into the repository pattern we've already established. In this article, we'll build on the existing structure and focus on using cache tags to group and clear related data more efficiently.
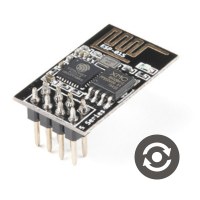
ESP8266 Firmware update
The ESP8266 is a popular Wi-Fi module used in many IoT projects. Keeping its firmware up-to-date ensures you have the latest features, security patches, and bug fixes. Updating the firmware might seem difficult, but it's quite straightforward once you understand the steps involved. In this article, we'll explore how to update the firmware of the ESP8266 module, a crucial task for maintaining optimal performance and security. This update process can be carried out either locally, using a USB connection, or remotely via cloud. We'll examine both methods to provide a comprehensive understanding of how to keep your ESP8266 up-to-date with the latest firmware version.
Recent articles

Keep your codebase clean with Git hooks
Every developer has been there: you push a commit, CI fails, and it turns out there was a linting error, a forgotten debug statement, or a test that nobody ran. Pre-commit hooks are the safety net that catches these problems before they ever leave your machine. They are not a complex feature or an advanced Git topic. They are just scripts, and once you understand how they work, you will find yourself reaching for them on every project.

Low power consumption mode in Arduino
Battery-powered Arduino projects have one common enemy: a board that drains power even when it has nothing to do. By default, Arduino runs at full speed continuously, burning through battery charge whether it's actively doing something or just waiting. Low power mode solves this by putting the microcontroller to sleep when it's idle, waking it up only when there's actual work to do. The concept is straightforward: the microcontroller spends most of its time asleep, wakes up to do something useful (take a sensor reading, send data, check a button), then goes back to sleep immediately.

Custom authentication in Laravel
Laravel ships with a solid authentication system out of the box, and most projects are well served by it. But there are situations where you need to authenticate users against something completely different: a legacy database, an external API, an LDAP server, or some other custom data source. Laravel's authentication system is built around a set of contracts and driver hooks that make this surprisingly straightforward to implement.